Jenkins CI/CD: A Comprehensive Guide
Learn why Jenkins CI/CD isn't ideal for continuous deployment and explore better alternatives to streamline your software delivery process.
Jenkins is great for CI, but using it for everything, including CD, can become a real headache. While Jenkins pipelines can handle continuous deployment, relying on them solely for complex deployments often creates a tangled mess of scripts and plugins. This post explores why separating your Jenkins CI/CD process into distinct CI and CD stages can lead to a more streamlined and scalable workflow, especially for growing teams and infrastructure. We'll cover the limitations of relying solely on Jenkins for CD, the hidden costs of maintaining a sprawling Jenkins setup, and alternative strategies for a more robust software delivery lifecycle.
It's not that it's impossible; some teams manage to make it work. However, the critical question is whether you should. More often than not, the answer tends to be no. While Jenkins excels in Continuous Integration (CI) scenarios, utilizing it for CI/CD proves to be a less-than-ideal workflow, often leading to more complications than initially anticipated.
We have seen this scenario repeatedly occur over the past two years of talking to customers: An engineering team uses Jenkins for testing code and building deployable artifacts (their CI process). They decide to employ Jenkins pipelines for executing CD, and while it seems promising initially, it introduces a host of problems and technical debt to the entire CI/CD process.
In the following sections, we'll delve into why Jenkins remains a popular solution, where it falls short in CD, and why it's advisable to move away from using Jenkins for CD capabilities.
Key Takeaways
- Jenkins is a powerful CI tool, but consider alternatives for CD: Jenkins's strengths lie in CI, but its architecture and reliance on plugins can create challenges for complex CD pipelines, especially as your infrastructure scales. Decoupling CI and CD allows for more specialized tooling and improved workflows.
- Modern CD tools streamline Kubernetes deployments: Solutions designed for cloud-native environments offer features like automated rollouts, simplified configuration, and better scalability, reducing the maintenance burden and improving deployment reliability.
- Plural offers a scalable, secure CD solution for Kubernetes: Plural integrates with existing CI setups and provides a robust platform for managing Kubernetes deployments across multiple environments, simplifying complex operations and freeing up engineering resources.
Why is Jenkins the Go-To CI/CD Tool?
Let's be clear that we don't discredit Jenkins as a tool. Jenkins stands out as an open-source automation server equipped with plugins for streamlined building, deploying, and automating projects. It remains a highly favored tool in the DevOps realm, boasting over 15 million downloads.
What many developers appreciate about Jenkins is its maturity and proven resilience. Designed with flexibility in mind, Jenkins provides an extensive Software Development Kit (SDK) covering virtually every imaginable aspect. Whether you're looking to oversee an AWS environment or integrate with GitHub, there's a plugin tailored for that specific purpose. While this adaptability has its drawbacks, it is the primary factor behind Jenkins' popularity and its success in numerous organizations.
Core Functionality and Benefits
Automating Software Delivery
Jenkins shines in automating software delivery with its robust CI capabilities. As TechTarget explains, Jenkins is a free and open-source tool that automates the process of building, testing, and deploying software. It acts as a central orchestrator, ensuring software is consistently updated and functions as expected. This automation is fundamental to CI/CD, enabling faster and more reliable software development.
Key Benefits
Jenkins's popularity comes from several key advantages. Its extensibility through a rich plugin ecosystem allows seamless integration with various software and systems. This flexibility lets teams create tailored pipelines to match their specific requirements. A large, active community provides ample support and resources. Its Java-based architecture ensures reliability and scalability for diverse projects.
Pipeline as Code
A defining feature of Jenkins is "Pipeline as Code." This allows developers to define their entire build, test, and deployment process in a `Jenkinsfile`, stored with the project's source code. This approach simplifies pipeline management, version control, and sharing across teams, promoting consistency and reproducibility. This codified approach to pipelines brings numerous benefits, including better collaboration and easier tracking of changes.
Community and Ecosystem
Open Source and Community Support
Jenkins thrives as a community-driven project, fostering collaboration and contributions from a global network of developers. This open-source nature encourages participation through code development, documentation, and sharing experiences. This collaborative environment ensures continuous improvement and provides a wealth of collective knowledge.
Extensive Resources
Learning Jenkins pipelines is made easier by the wealth of available resources. The Jenkins website offers tutorials and comprehensive documentation within the Pipeline plugin's source code. A repository of example Pipeline scripts provides practical examples for various use cases. These resources offer valuable guidance and support for users of all skill levels.
Jenkins CI/CD: Where Does it Fail?
To be blunt, Jenkins is starting to show its age as software. Originally developed in 2004, it wasn't designed to be cloud-native. Although developers and DevOps teams have found ways to make it work, its architecture, rooted in a master node and multiple build agents, reflects an outdated model from the era of data centers and static servers.
While this approach isn't necessarily bad, the reliance on plugins for workarounds introduces additional configurations, often seen as a hassle. For instance, configuring containers with the Jenkins Kubernetes plugin involves working with YAML inside a Groovy file, increasing the risk of errors. The variety in plugin syntax further complicates matters.
Managing Jenkins is considered challenging, with its requirement for Groovy scripting adding complexity compared to more modern tools. Despite the usefulness of Jenkins' SDKs, some plugins are limited and just have basic functionality. That’s fine until you realize that most plugins are often not well documented and you need to script your way through a majority of use cases. On top of that most users complain about buggy plugins that are a hassle to manage from a dependency standpoint. Some plugins unfortunately can’t be patched for security vulnerabilities due to inter-dependencies.
The user interface is notably outdated, demanding significant human resources for operation. Despite attempts to reduce script reliance, Jenkins remains script-centric. This results in the DevOps team being burdened with maintaining infrastructure, updating plugins, and troubleshooting.
In reality, it’s estimated that sustaining Jenkins requires the daily efforts of 2 to 5 engineers. While valuable and proficient in various tasks, the limitations of relying solely on Jenkins become evident as operations expand, leading to increased maintenance, operational challenges, and potential disruptions.
Scaling Challenges
As your engineering organization grows, so does the complexity of managing your CI/CD pipelines. While Jenkins can handle simple deployments, it struggles at scale. We've seen firsthand how relying solely on Jenkins for CD can become a bottleneck. Sustaining a Jenkins instance often requires the daily effort of several engineers. These engineers, while valuable, end up spending their time maintaining Jenkins instead of focusing on strategic initiatives. This operational overhead becomes a significant challenge as your infrastructure and team expand.
Imagine trying to manage hundreds of deployments across multiple environments with a tool primarily designed for single-server deployments. The plugin-based architecture, while flexible, becomes a source of friction. Each plugin introduces potential points of failure and requires dedicated maintenance. Troubleshooting becomes a nightmare as you try to isolate issues across a complex web of interconnected plugins. This is where Jenkins starts to show its limitations, hindering your ability to scale efficiently.
Technology
Jenkins, initially developed in 2004, wasn't designed for today's cloud-native world. Its architecture, centered around a master node and build agents, reflects an older model from the era of data centers and static servers. While it can be adapted to work in modern cloud environments, this often requires workarounds and plugins, adding another layer of complexity. For example, configuring containers with the Jenkins Kubernetes plugin involves working with YAML inside a Groovy file, a process prone to errors and difficult to manage at scale.
The user interface, while functional, feels outdated and can be cumbersome to use. Despite efforts to reduce reliance on scripting, Jenkins remains largely script-centric, particularly when dealing with complex pipeline configurations. This means your DevOps team spends valuable time writing and maintaining Groovy scripts, instead of focusing on higher-value tasks. Furthermore, many plugins, while offering extended functionality, are often poorly documented and can introduce instability due to interdependencies and the potential for conflicting configurations. This can lead to security vulnerabilities if plugins can't be patched due to these dependencies. Ultimately, these technological limitations make scaling Jenkins a significant undertaking, often requiring substantial engineering effort and resources.
Moving Your CI/CD Off Jenkins: When Does it Make Sense?
We firmly believe that software delivery and deployment should be separate from your CI provider, which is usually purpose-built for running unit tests and compiling build artifacts. There are some major motivations for this separation, among them being:
- Deployment is frequently a much longer running process than a standard code change, encompassing staged releases across multiple environments with multiple rounds of integration testing.
- A separate CD system can make it easy to manage drift in microservice dependencies by allowing them to be tested in tandem and rolled back independently.
- Separating CD enhances your security posture by not requiring master creds in a building service like Jenkins or a cloud service like Circle-CI.
A central CD service drastically simplifies managing polymorphic infrastructure providers, as a pull-based architecture naturally can extend to multi-cloud or on-prem delivery models.
Jenkins functions as a CI server, heavily dependent on scripts. The Jenkins pipeline functionality, consisting of a suite of plugins, facilitates the implementation and integration of CD pipelines within Jenkins. This situation presents challenges in establishing a smooth and comprehensive CI/CD pipeline.
Putting aside Jenkins plugins, let’s quickly break down a few core concepts of a deployment pipeline:
- Artifacts
- Applications or services
- Secrets
- Deployment workflow
- Stages
- Ability to rollback
- Software release strategy (Blue/Green, Canary, etc.)
- Tests and tooling (security and monitoring)
- User Groups & Users (RBAC)
Jenkins pipeline functionality contains none of those out-of-the-box. Instead, you have to write custom scripting to manage or perform all the above tasks. You get the point, Jenkins pipelines are just another way of hardcoding together a solution with scripts.
Your and your team's time is far too valuable to spend it maintaining deployment pipelines. The reality is that scripting together your pipeline introduces more complexity, which increases the chances of pipelines failing.
Sure, if you want to you can manually script a Canary deployment to a Kubernetes cluster by heavily editing some Jenkinsfiles, but it’s not easy and ultimately a pain. Remember what was mentioned earlier; just because you can, doesn’t mean you should.
Jenkins' Role in CI/CD Pipelines
CI/CD Process
Jenkins is a free and open-source automation server that plays a crucial role in CI/CD pipelines. It automates the process of building, testing, and deploying software, ensuring code changes are integrated frequently and reliably. Think of it as an orchestrator that keeps your software development process flowing smoothly. It's a key component of CI/CD, a set of practices designed to make software development faster and more reliable. For a deeper dive into Jenkins and its functionality, check out this TechTarget article on Jenkins.
Jenkinsfiles
One of the core features of Jenkins is its support for "Pipeline as Code" through Jenkinsfiles. A Jenkinsfile is a text file, often written in Groovy, that describes your entire CI/CD pipeline as code. This file defines the different stages of your pipeline, such as building, testing, and deploying. Storing the Jenkinsfile with your project's code makes it version-controlled and easy to manage alongside your application's source code. This approach simplifies collaboration and ensures that your pipeline definition evolves with your project.
Jenkins Pipeline Stages
A typical Jenkins pipeline consists of several key stages. These stages often include Checkout, Build, Test, and Deploy. The Checkout stage retrieves the source code from your version control system. The Build stage compiles the code, while the Test stage runs automated tests to identify bugs. Finally, the Deploy stage releases the software to the target environment. This structured approach ensures consistent and repeatable deployments.
Comparison with Other CI/CD Tools
Alternative CI/CD Platforms
The CI/CD landscape offers several alternatives to Jenkins, each with its own strengths and weaknesses. Popular options include GitHub Actions, GitLab CI/CD, and CircleCI. Most CI/CD tools share similar core functionalities. The best choice often depends on your existing toolchain and specific requirements. For example, if your team primarily uses GitHub, GitHub Actions might be a natural fit.
Existing Toolchains
Leveraging your existing toolchain can significantly simplify your CI/CD workflow. If your team already uses platforms like GitHub or GitLab, their built-in CI/CD systems can be the most straightforward approach. These integrated solutions offer a seamless experience, minimizing context switching and simplifying workflow management. This integration reduces friction and accelerates adoption, as highlighted in this Reddit discussion on CI/CD platforms.
Specific Use Cases
While newer CI/CD tools offer compelling features, Jenkins remains a popular choice for complex or highly customized pipelines. Its extensive plugin ecosystem and flexibility allow it to handle diverse scenarios that might be challenging for other platforms. This makes Jenkins suitable for organizations with unique workflows or legacy systems. However, this flexibility comes at a cost, as managing numerous plugins can introduce complexity and maintenance overhead.
Maintenance Overhead
One of the key considerations when evaluating Jenkins is its maintenance overhead. Managing a Jenkins server, including plugin updates, security patches, and infrastructure management, can require significant resources. Maintaining a Jenkins instance can demand the dedicated effort of multiple engineers, impacting overall team productivity and potentially diverting resources from other critical tasks. For teams looking to streamline operations and reduce maintenance burden, exploring alternative CI/CD solutions might be beneficial. This TechTarget article provides further insights into the operational aspects of Jenkins.
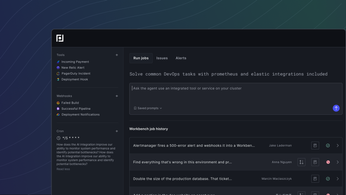
Plural: A Modern Alternative to Jenkins CI/CD
We believe that CDs shouldn't be challenging. You shouldn’t be coding and maintaining your CD process as your applications and services evolve. There are plenty of CD tools on the market that integrate and complement Jenkins for CI.
At Plural we evolved our product to easily integrate with CI tools such as Jenkins. This model allows you to let your CI system do what it does best, test code, and build deployable artifacts, and then allow our products CD capabilities to handle the longer-duration and security-intensive task of deployment from there.
Our CD capabilities are based on a scalable, secure, agent-based pull architecture. It doesn't require direct access to any of the clusters it deploys to, meaning it can manage workloads in any cloud, on-prem, on the edge, or even on a local laptop running KIND.
General Information about Jenkins
History and Management
Jenkins, the robust open-source automation server, evolved from the Hudson project after a trademark dispute. Now overseen by the Continuous Delivery Foundation (CDF), a non-profit championing open-source CI/CD tooling, Jenkins benefits from a dedicated community ensuring its ongoing development and relevance in the software development world.
Advantages and Disadvantages
Plugin Ecosystem
Jenkins shines with its rich plugin ecosystem, offering extensions that enhance its core functionality. These plugins enable seamless integration with a diverse range of tools and technologies, empowering developers to tailor their CI/CD pipelines and connect Jenkins effortlessly with existing workflows. Need to connect with Git, AWS, Azure, or various testing frameworks? There's likely a Jenkins plugin ready to simplify the integration.
Flexibility and Community Support
As an open-source project, Jenkins thrives on a vibrant and supportive community. This active community, boasting millions of users globally, provides a wealth of knowledge, readily available resources, and prompt assistance for troubleshooting and configuration challenges. This strong community backing significantly contributes to Jenkins's enduring popularity and continued relevance in the CI/CD landscape.
Setup and Maintenance Complexity
Jenkins's flexibility, while advantageous, introduces complexity in setup and maintenance. Managing a Jenkins server often demands specialized expertise and dedicated engineering resources. Tasks such as configuring plugins, scripting complex pipelines with Groovy, and maintaining server stability can consume substantial time and effort. As explored in our analysis of migrating from Jenkins, upkeep can require the daily focus of multiple engineers, potentially diverting them from other mission-critical projects.
The Importance of Separating CI and CD
Reasons for Separation
While Jenkins can manage both Continuous Integration (CI) and Continuous Delivery (CD), separating these processes often yields a more streamlined and robust workflow. CI, centered on building and testing code changes, typically involves shorter, more frequent cycles. CD, conversely, focuses on deploying code across various environments, often involving complex procedures like staged rollouts and comprehensive integration testing. As highlighted in our previous discussion, deployments can be lengthy operations, potentially spanning multiple environments and demanding extensive testing. Decoupling CI and CD allows for optimized management of each process, minimizing bottlenecks and disruptions.
Fundamental Steps for Successful CI/CD
A successful CI/CD pipeline hinges on automating the core stages of software delivery: building the code, executing automated tests, and deploying the application across different environments. Visualize the CI/CD pipeline as an automated roadmap, guiding your software from initial code commit to final production release. Each stage acts as a quality gate, catching potential issues early and ensuring that only thoroughly vetted code reaches end-users.
Benefits of CI/CD
Implementing a robust CI/CD pipeline delivers numerous advantages. It accelerates the software development lifecycle, enabling teams to release features and updates with greater frequency. By automating testing and deployment, CI/CD facilitates early bug detection and resolution, resulting in higher software quality and reduced downtime. This rapid feedback loop also empowers teams to respond swiftly to evolving market demands and customer feedback.
CI/CD and DevOps
CI/CD is a fundamental pillar of the DevOps philosophy, which prioritizes collaboration and shared ownership between development and operations teams. By automating the processes bridging these two functions, CI/CD promotes smoother transitions and reduces friction. This enhanced collaboration fosters a more streamlined workflow, faster releases, and ultimately, a more efficient and high-performing software development organization.
Related Articles
- Stop using Jenkins for Continuous Deployment (CD)
- Continuous Deployment: A Comprehensive Guide for 2024
Frequently Asked Questions
Why shouldn't I use Jenkins for CD if it's already my CI tool?
While using Jenkins for both CI and CD might seem convenient, it often creates more problems than it solves. Jenkins excels at CI, where tasks are typically short-lived and focused on building and testing. CD, however, involves longer processes like deployments, staged rollouts, and integration testing. Managing these distinct workflows within a single Jenkins instance can lead to bottlenecks and complexity, especially as your infrastructure and team grow. A dedicated CD tool offers better scalability, security, and management of these longer, more intricate processes.
What are the main challenges of scaling Jenkins for CD?
Scaling Jenkins for CD becomes increasingly difficult due to its plugin-based architecture and reliance on scripting. Each plugin adds potential points of failure and requires maintenance. Troubleshooting complex pipelines strung together with various plugins becomes a significant challenge. Moreover, managing a large Jenkins instance often demands substantial engineering resources, diverting valuable time from strategic projects.
What are some better alternatives for CD?
Modern CD tools like Plural, GitHub Actions, GitLab CI/CD, and CircleCI offer more streamlined and scalable solutions compared to Jenkins for CD. These tools are often designed with cloud-native environments in mind and provide features like automated deployments, pipeline management, and integration with existing toolchains. Choosing the right tool depends on your specific needs and existing infrastructure.
What are the core benefits of separating CI and CD?
Separating CI and CD allows each process to be optimized independently. CI focuses on rapid feedback cycles for building and testing code, while CD handles the more complex and security-sensitive aspects of deployment. This separation improves scalability, simplifies troubleshooting, and enhances security by avoiding the need to grant CI tools access to deployment environments. It also allows for more sophisticated deployment strategies like canary deployments and blue/green deployments.
How does Plural work with my existing CI setup?
Plural integrates with CI tools like Jenkins, allowing you to leverage your existing CI processes while benefiting from Plural's advanced CD capabilities. Plural uses a secure, agent-based pull architecture that doesn't require direct access to your clusters. This approach simplifies management of multi-cloud and on-premises deployments while enhancing security. Plural handles the complexities of deployment, freeing your CI system to focus on what it does best: building and testing code.
Newsletter
Join the newsletter to receive the latest updates in your inbox.